Forward Secrecy and Ephemeral Keys … Guarding Against Data Breaches in the Future and the Past | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium
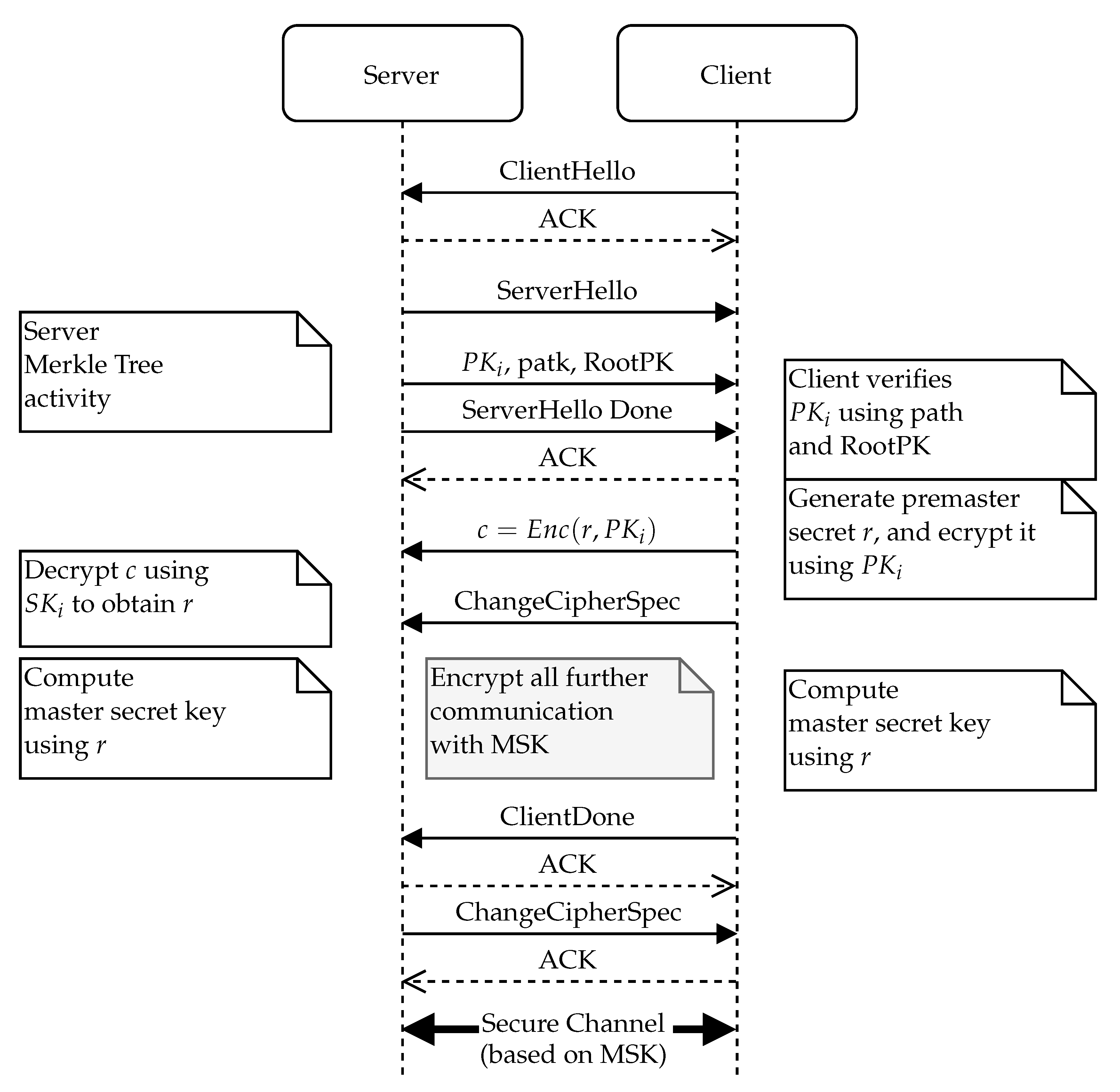
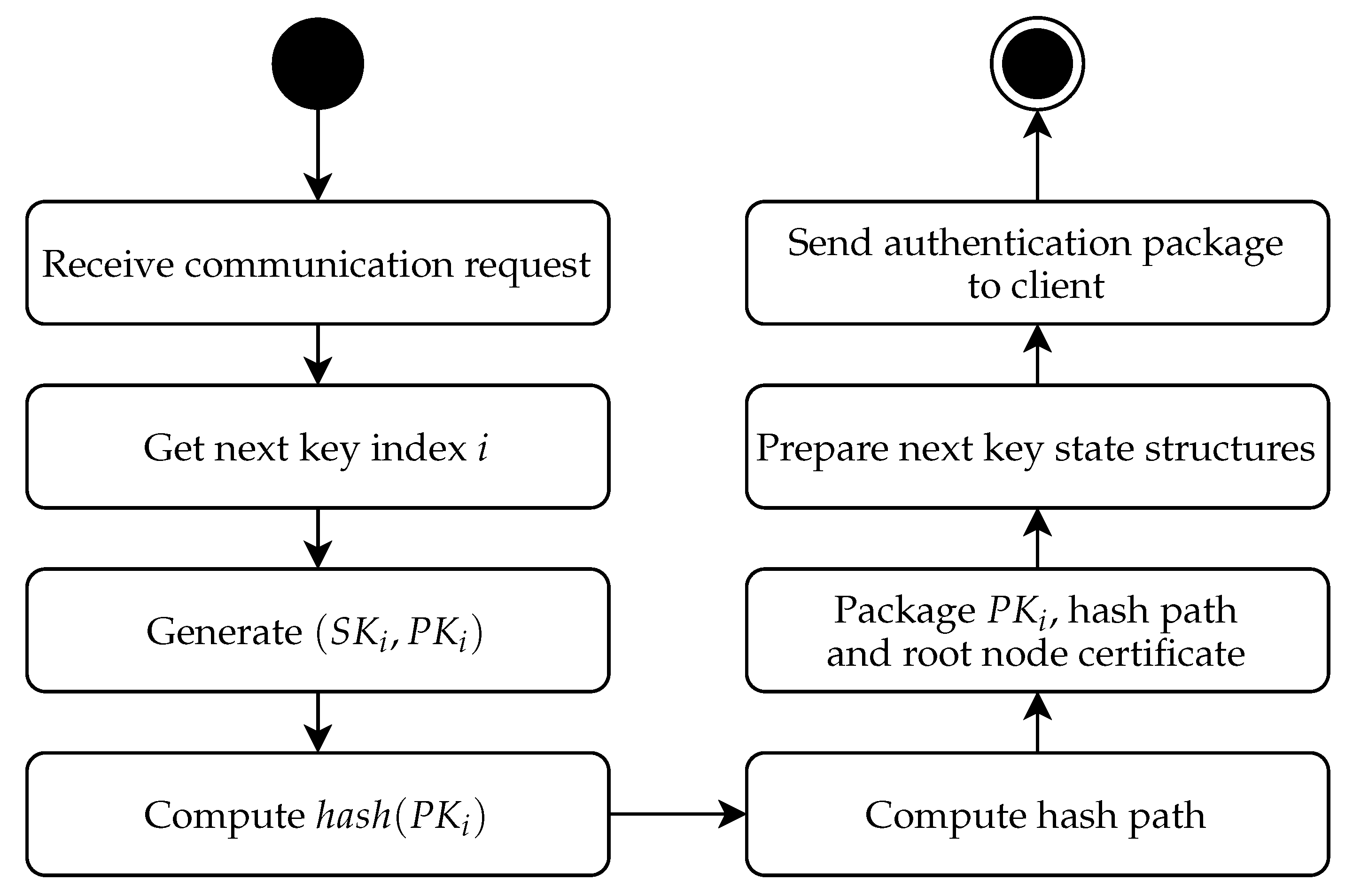
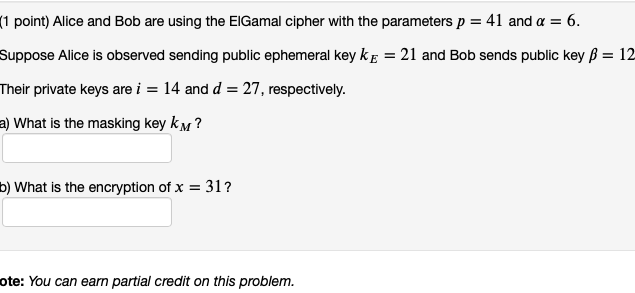
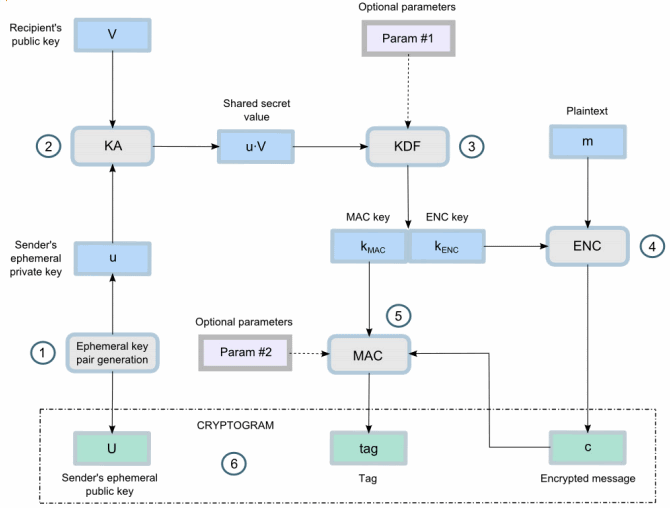
Sensors | Free Full-Text | Ephemeral Keys Authenticated with Merkle Trees and Their Use in IoT Applications








![BUG] using expired Ephemeral Key · Issue #6532 · stripe/stripe-android · GitHub BUG] using expired Ephemeral Key · Issue #6532 · stripe/stripe-android · GitHub](https://user-images.githubusercontent.com/6266608/231778740-66f998ad-6073-4230-859c-14ba033c7e17.jpeg)